首页 > 代码库 > Docker私有仓库Registry认证搭建
Docker私有仓库Registry认证搭建
前言:
首先,Docker Hub是一个很好的用于管理公共镜像的地方,我们可以在上面找到想要的镜像(Docker Hub的下载量已经达到数亿次);而且我们也可以把自己的镜像推送上去。但是,有的时候我们的使用场景需要拥有一个私有的镜像仓库用于管理自己的镜像,这个时候我们就通过Registry来实现此目的。本文详细介绍了本地镜像仓库Docker Registry及Auth Server认证搭建。
集群环境:
系统 | 主机名 | IP地址(Host-Only) | 描述 |
Centos7.2.1511 | controller | 192.168.200.9 | Docker、Registry、Auth-server |
Centos7.2.1511 | compute | 192.168.200.10 | Docker |
1.下载所需要的镜像
# controller节点: docker pull registry docker pull cesanta/docker_auth docker pull sspaas.net/renyf/mongodb:3.2
2.安装所需软件
# controller节点: yum -y install epel-release yum -y install nginx ntp httpd-tools
3.修改hosts文件
cat >> /etc/hosts << EOF 192.168.200.9 controller registry.testcloud.com 192.168.200.10 compute EOF
3.生成自签证书(私钥文件及根证书文件)
# controller节点: mkdir -p /auth_server/ssl cd /auth_server/ssl openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout server.key -out server.pem -subj"/C=CN/ST=state/L=city/O=xxx/OU=registry.testcloud.com"
4.使用htpasswd生成账户信息(密码随意指定,我这里为123456)
# controller节点: cd /auth_server htpasswd -Bc.passwd renyf
5.启动mongodb数据库
这里采用容器做了mongodb数据库,当然你也可以本地去搭建使用mongodb(此处省略)
# controller节点: docker run -d -p 27017:27017 -p 28017:28017 --name mongo -e MONGODB_PASS=a123456 sspaas.net/renyf/mongodb:3.2
6.进入mongodb创建我们所需要的数据库,用户及其权限
# controller节点:
docker exec -it mongo mongo admin -u admin -p a123456
# 创建数据库
MongoDB Enterprise> use registry_auth
# 创建数据库用户及授权
MongoDB Enterprise> db.createUser({user: ‘renyf‘, pwd: ‘a666666‘, roles:[{role:‘dbOwner‘,db:‘registry_auth‘}]})7.现在我们把之前使用htpasswd创建的用户信息写到数据库中(密码为:123456)
# controller节点: cat /auth_server/.passwd
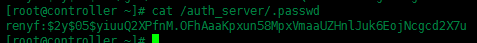
# controller节点:
# 在数据库user表中创建用户
MongoDB Enterprise > db.user.insert({username:‘renyf‘, password:‘$2y$05$yiuuQ2XPfnM.OFhAaaKpxun58MpxVmaaUZHnlJuk6EojNcgcd2X7u‘})
# 在数据库acl表中设置用户权限
MongoDB Enterprise> db.acl.insert({‘seq‘: 1, ‘match‘: {‘account‘: ‘/.+/‘, ‘name‘:‘${account}/*‘}, ‘actions‘: [‘*‘]})好的,到这里我们就完成了对registry用户及用户权限的配置
8.编写auth_server的config配置文件
# controller节点:
vim /auth_server/config/auth_config.yml
内容如下:
server: # Server settings.
# Address to listen on.
addr: ":5001"
# TLS certificate and key.
certificate: "/ssl/server.pem"
key: "/ssl/server.key"
token: # Settings for the tokens.
issuer: "Auth Service" # Must match issuer in the Registry config.
expiration: 900
# Static user map.
users:
"": {} # Allow anonymous (no "dockerlogin") access.
mongo_auth:
dial_info:
addrs: ["192.168.200.9:27017"]
timeout: "10s"
database: "registry_auth"
username: "renyf"
password: "a666666"
collection: "user"
acl_mongo:
dial_info:
addrs: ["192.168.200.9:27017"]
timeout: "10s"
database: "registry_auth"
username: "renyf"
password: "a666666"
collection: "acl"
cache_ttl: "1m"9.现在我们启动auth_server
# controller节点: docker run -d -p 5001:5001 --restart=always --name docker_auth -v /auth_server/config:/config:ro -v /var/log/docker_auth:/logs -v /auth_server/ssl:/ssl cesanta/docker_auth /config/auth_config.yml
10.启动registry
# controller节点: docker run -d -p 5000:5000 --restart=always --name registry -e REGISTRY_STORAGE_FILESYSTEM_ROOTDIRECTORY=/var/lib/registry -e REGISTRY_AUTH=token -e REGISTRY_AUTH_TOKEN_REALM=https://registry.testcloud.com:5001/auth -e REGISTRY_AUTH_TOKEN_SERVICE="Docker registry" -e REGISTRY_AUTH_TOKEN_ISSUER="Auth Service" -e REGISTRY_AUTH_TOKEN_ROOTCERTBUNDLE=/ssl/server.pem -v /auth_server/ssl:/ssl -v /root/docker_registry/data:/var/lib/registry registry
11.现在我们再给registry加上nginx代理
# controller节点:
# 编辑nginx配置文件
vim /etc/nginx/nginx.conf
# 内容如下:
# For moreinformation on configuration, see:
# * Official English Documentation:http://nginx.org/en/docs/
# * Official Russian Documentation:http://nginx.org/ru/docs/
user nginx;
worker_processes auto;
error_log /var/log/nginx/error.log;
pid /run/nginx.pid;
# Load dynamicmodules. See /usr/share/nginx/README.dynamic.
include /usr/share/nginx/modules/*.conf;
events {
worker_connections 1024;
}
http {
log_format main ‘$remote_addr - $remote_user[$time_local] "$request" ‘
‘$status $body_bytes_sent"$http_referer" ‘
‘"$http_user_agent" "$http_x_forwarded_for"‘;
access_log /var/log/nginx/access.log main;
sendfile on;
tcp_nopush on;
tcp_nodelay on;
keepalive_timeout 65;
types_hash_max_size 2048;
include /etc/nginx/mime.types;
default_type application/octet-stream;
# Load modular configuration files from the/etc/nginx/conf.d directory.
# Seehttp://nginx.org/en/docs/ngx_core_module.html#include
# for more information.
include /etc/nginx/conf.d/*.conf;
upstream docker-registry{
server 192.168.200.9:5000;
}
server {
listen 80;
listen 443;
server_name registry.testcloud.com;
root /usr/share/nginx/html;
ssl on;
ssl_certificate /auth_server/ssl/server.pem;
ssl_certificate_key /auth_server/ssl/server.key;
proxy_set_header Host $http_host;
proxy_set_header X-Real-IP $remote_addr;
client_max_body_size 0; # disable any limits to avoid HTTP 413 forlarge image uploads
chunked_transfer_encoding on;
add_header‘Docker-Distribution-Api-Version‘ ‘registry/2.0‘ always;
# Load configuration files for thedefault server block.
include /etc/nginx/default.d/*.conf;
location / {
proxy_pass http://docker-registry;
proxy_set_header Host $http_host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_headerX-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_headerX-Forwarded-Proto $scheme;
proxy_read_timeout 900;
}
error_page 404 /404.html;
location = /40x.html {
}
error_page 500 502 503 504 /50x.html;
location = /50x.html {
}
}
}12.启动nginx
# controller节点: systemctl start nginx
好了,这里我们服务已经基本搭建完成了。
客户端
因为是自签名证书,所以我们要在docker的配置里面添加信任
# compute节点: vim /lib/systemd/system/docker.service # 添加内容如下: --insecure-registry registry.testcloud.com:5000

# compute节点: # 重新启动docker服务 systemctl daemon-reload && systemctl restart docker
验证:
registry登录验证:
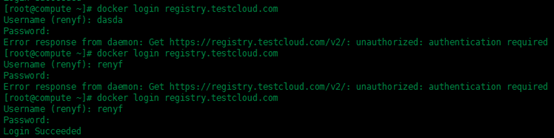
如上图所示,你的用户不存在数据库中,或者用户名存在但是密码错误是登录不上去的。
现在我们来更改镜像名,来上传镜像验证
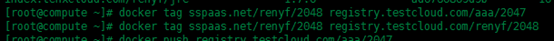

此时第一个tag更改的镜像命名中用户名为aaa并不是登录成功的用户名renyf,所以这里上传时会出现认证失败的报错,上传不上去,接下来我们换成与用户名相匹配的镜像来上传
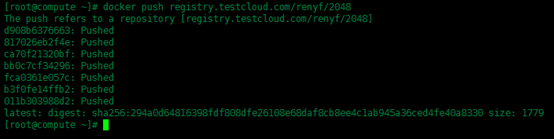
这次就上传成功了。当然,下载镜像也一样,此处就不提供图了。
参考文档:https://github.com/cesanta/docker_auth/blob/master/docs/Backend_MongoDB.md
本文出自 “Renyf” 博客,请务必保留此出处http://renyongfan.blog.51cto.com/11693321/1955214
Docker私有仓库Registry认证搭建
