首页 > 代码库 > 利用OpenSSL构建私有CA
利用OpenSSL构建私有CA
实验环境:
CentOS release 6.6(Final) 两台
IP地址:
服务器端:172.16.31.3
客户端:172.16.31.2
查看系统书否已安装openSSL执行命令“rpm –qa openssl”
[root@CA ~]# rpm -qa openssl
openssl-1.0.1e-30.el6.x86_64
OpenSSL本身是一种ssl的开源方式用以实现https的数据加密传输,但OpenSSL的功能绝不仅限于此,OpenSSL提供了两个重要的库:一个是libcrypto,被称为通用加密库,提供了各种加密函数,任何程序都可以调用此库来实现加密功能;另一个是libssl,是一种基于会话的、实现了身份认证、数据机密性和会话完整性的TLS/SSL协议库。另外OpenSSL还提供了一个命令行工具就叫OpenSSL,是一个多用途的命令行工具,提供了很多子命令,调用不同的子命令可以实现不同的功能,诸如单向加密、对称加密和非对称加密、生成密钥对等。OpenSSL本身并没有提供类似“--help”之类的帮助命令,输入OpenSSL后跟任意一个OpenSSL不能识别的命令就会显示输出所有子命令,比如输入“openssl ?”就会看到所有子命令。
下面介绍使用openssl模拟证书颁发机构构建私有CA。
一.配置OpenSSL配置文件
1.配置OpenSSL的配置文件。
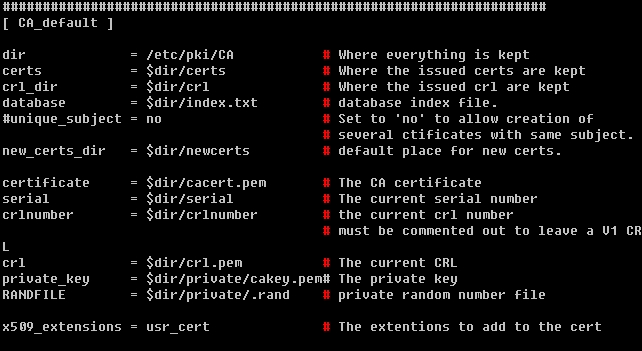
可以编辑/etc/pki/tls/openssl.cnf
将其中的“[CA_default ]”段中定义的CA工作目录默认为“/etc/pki/CA”,证书默认有效期等信息根据具体应用环境更改。
在[ req_distinguished_name ]段中设置一下默认的国家代码、所属省份、市区、公司名称、所属部门等信息。
将国家,省份,城市,组织名称写好,方便下次生成CA时更便捷。
二.创建CA自签署证书
1.为CA生成私钥密钥
#cd/etc/pki/CA
#mkdir private
# (umask 077 ; openssl genrsa -out private/cakey.pem 2048)
Generating RSA private key, 2048 bit longmodulus
..........................................................................................+++
...............................................+++
e is 65537 (0x10001)
命令加括号表示命令在子shell中执行,设定子shell的umask为077,子shell生成的文件将是600的权限,-out指定输出文件位置,2048为密钥长度。
2.创建所需目录和文件
创建所需目录
#mkdir certs newcerts crl
创建证书检索文:
#touch index.txt
创建证书序列号文件并赋初值:
#touch serial
#echo 01 > serial
# ls
cacert.pem certs crl index.txt newcerts private serial
3.创建自签署证书,如果没配置/etc/pki/tls/openssl文件,命令创建自签署证书如下所示:
# opensslreq -new -x509 -keyprivate/cakey.pem -days 35600 -out cacert.pem
You are about to be asked to enterinformation that will beincorporated
into your certificate request.
What you are about to enter is what iscalled a Distinguished Nameor a DN.
There are quite a few fields but you canleave some blank
For some fields there will be a defaultvalue,
If you enter ‘.‘, the field will be leftblank.
-----
Country Name (2 letter code) [CN]:CN #国家名称缩写
State or Province Name (full name) []:HA #省份缩写
Locality Name (eg, city) [Default City]:ZZ #省会缩写
Organization Name (eg, company) [DefaultCompany Ltd]:Test #组织或公司名称
Organizational Unit Name (eg, section)[]:OPS #部门
Common Name (eg, your name or your server‘shostname) []:CA.test.com #主机名
Email Address []:ca@test.com #邮件地址
至此CA服务器端创建完成。
三.给节点颁发证书
下面介绍使用此CA为其他应用签署证书。以httpd服务为例:
1.节点申请证书,在申请证书的主机上进行,我这里实验的是http服务,所以我的证书在服务路径下
# cd /etc/httpd/conf/
创建一个目录来保持私钥和证书申请文件
#mkdir certs
#cd /etc/httpd/conf/certs
为httpd服务生成私钥:
# (umask 077 ; openssl genrsa -out httpd.key 1024)
Generating RSA private key, 1024 bit longmodulus
.............................++++++
.++++++
e is 65537 (0x10001)
# ll
total 4
-rw------- 1 root root 887 Dec 8 14:00 httpd.key
2.生成签署请求文件
我们直接从CA服务器提取Openssl.cnf文件
[root@stu1 certs]# scp root@172.16.31.3:/etc/pki/tls/openssl.cnf./
然后生成CA证书签署请求文件:
其中很多值都已经写好了
[root@stu1 certs]# scp httpd.csr172.16.31.3:/etc/pki/CA/certs/httpd.csr
root@172.16.31.3‘s password:
httpd.csr: No such file or directory
[root@stu1 certs]# openssl req -new -keyhttpd.key -out httpd.csr -days 35600
You are about to be asked to enterinformation that will beincorporated
into your certificate request.
What you are about to enter is what iscalled a Distinguished Nameor a DN.
There are quite a few fields but you canleave some blank
For some fields there will be a defaultvalue,
If you enter ‘.‘, the field will be leftblank.
-----
Country Name (2 letter code) [CN]:
State or Province Name (full name) [HA]:
Locality Name (eg, city) [ZZ]:
Organization Name (eg, company) [Test]:
这里的名称必须跟服务器输入的名称一致
Organizational Unit Name (eg, section)[]:OPS
Common Name (eg, your name or your server‘shostname) []:stu1.test.com
这里的名称可以是你的主机名称或者服务器的主机名称
EmailAddress []:stu1@test.com
Please enter the following ‘extra‘attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
[root@stu1 certs]# ls
httpd.csr httpd.key
查看一下申请文件
[root@stu1 certs]# cat httpd.csr
-----BEGIN CERTIFICATE REQUEST-----
MIIBujCCASMCAQAwejELMAkGA1UEBhMCQ04xCzAJBgNVBAgMAkhBMQswCQYDVQQH
DAJaWjENMAsGA1UECgwEVGVzdDEMMAoGA1UECwwDT1BTMRYwFAYDVQQDDA1zdHUx
LnRlc3QuY29tMRwwGgYJKoZIhvcNAQkBFg1zdHUxQHRlc3QuY29tMIGfMA0GCSqG
SIb3DQEBAQUAA4GNADCBiQKBgQCd7fN0pVbrqu8LpgbQuSNs/Q7ddG7/NKYPJOyl
cGx+B9znApdUw9tF2Zr5xAtwghJS1rVyoczqy5YAmVnTIAwoKaEatqt95B8DNfRl
4gGn0LBOLf3V8oR/nYOQwig354ebUtn/ktkoBkI80qdXblAiojIHa/5Ucpak23VW
jSKU+wIDAQABoAAwDQYJKoZIhvcNAQEFBQADgYEAFJc2+os1BYxZvmZqN0D/i2R0
PUaTSZzbV5o0cSOrHZpUhTBQ9LJw0JG43eGQlFoFndyOWBhdptHl+KNg5c/VIBs7
0Vd0fyM3CsoR2ep8PVT1sCWev3LTghpu5WkomGgBpWjTi+SBb4/Mp7Si0LnJfN+u
W3nJz6oNtYMHHckdL0g=
-----END CERTIFICATE REQUEST-----
3.将CA证书申请文件发送给CA
[root@stu1 certs]# scp httpd.csr172.16.31.3:/etc/pki/CA/certs/httpd.csr
root@172.16.31.3‘s password:
httpd.csr 100% 680 0.7KB/s 00:00
检查一下传输成功与否:
[root@CA CA]# ls certs/
httpd.csr
[root@CA CA]# cat certs/httpd.csr
-----BEGIN CERTIFICATE REQUEST-----
MIIBujCCASMCAQAwejELMAkGA1UEBhMCQ04xCzAJBgNVBAgMAkhBMQswCQYDVQQH
DAJaWjENMAsGA1UECgwEVGVzdDEMMAoGA1UECwwDT1BTMRYwFAYDVQQDDA1zdHUx
LnRlc3QuY29tMRwwGgYJKoZIhvcNAQkBFg1zdHUxQHRlc3QuY29tMIGfMA0GCSqG
SIb3DQEBAQUAA4GNADCBiQKBgQCd7fN0pVbrqu8LpgbQuSNs/Q7ddG7/NKYPJOyl
cGx+B9znApdUw9tF2Zr5xAtwghJS1rVyoczqy5YAmVnTIAwoKaEatqt95B8DNfRl
4gGn0LBOLf3V8oR/nYOQwig354ebUtn/ktkoBkI80qdXblAiojIHa/5Ucpak23VW
jSKU+wIDAQABoAAwDQYJKoZIhvcNAQEFBQADgYEAFJc2+os1BYxZvmZqN0D/i2R0
PUaTSZzbV5o0cSOrHZpUhTBQ9LJw0JG43eGQlFoFndyOWBhdptHl+KNg5c/VIBs7
0Vd0fyM3CsoR2ep8PVT1sCWev3LTghpu5WkomGgBpWjTi+SBb4/Mp7Si0LnJfN+u
W3nJz6oNtYMHHckdL0g=
-----END CERTIFICATE REQUEST-----
4.CA签署证书
ca表示签署,-in 指定申请签署文件,-out 指定输出路径和文件名,-days 35600 指定证书有效期
[root@CACA]# openssl ca -in /etc/pki/CA/certs/httpd.csr -out/etc/pki/CA/certs/httpd.crt-days 35600
Using configuration from/etc/pki/tls/openssl.cnf
Check that the request matches thesignature
Signature ok
Certificate Details:
Serial Number: 1 (0x1)
Validity
NotBefore: Dec 8 06:33:10 2014GMT
NotAfter : May 28 06:33:10 2112 GMT
Subject:
countryName = CN
stateOrProvinceName = HA
organizationName = Test
organizationalUnitName = OPS
commonName = stu1.test.com
emailAddress =stu1@test.com
X509v3 extensions:
X509v3Basic Constraints:
CA:FALSE
NetscapeComment:
OpenSSL Generated Certificate
X509v3Subject Key Identifier:
9E:C9:9A:33:FC:91:A9:34:CA:16:E5:79:5E:11:5B:BB:BA:61:65:75
X509v3Authority Key Identifier:
keyid:CC:33:C7:0E:59:10:F7:14:AF:F6:5E:85:9E:24:D6:81:14:3F:F5:47
Certificate is to be certified until May 2806:33:10 2112 GMT(35600 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified,commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
4.把签署好的证书发送给申请者
[root@CA CA]# scp certs/httpd.crt172.16.31.2:/etc/httpd/conf/certs/
The authenticity of host ‘172.16.31.2(172.16.31.2)‘ can‘t beestablished.
RSA key fingerprintisa4:1d:39:08:30:8c:17:fd:2a:8e:db:da:15:3f:08:e4.
Are you sure you want to continue connecting(yes/no)? yes
Warning: Permanently added ‘172.16.31.2‘(RSA) to the list of knownhosts.
root@172.16.31.2‘s password:
httpd.crt 100%3785 3.7KB/s 00:00
在客户端查看证书:
[root@stu1 certs]# ls
httpd.crt httpd.csr httpd.key
[root@stu1 certs]# openssl x509 -in httpd.crt -noout -text
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 1 (0x1)
Signature Algorithm: sha1WithRSAEncryption
Issuer: C=CN, ST=HA,L=ZZ, O=Test, OU=OPS, CN=CA.test.com/emailAddress=ca@test.com
Validity
NotBefore: Dec 8 06:33:10 2014GMT
NotAfter : May 28 06:33:10 2112 GMT
Subject: C=CN, ST=HA,O=Test, OU=OPS,CN=stu1.test.com/emailAddress=stu1@test.com
Subject Public Key Info:
PublicKey Algorithm: rsaEncryption
Public-Key: (1024 bit)
Modulus:
00:9d:ed:f3:74:a5:56:eb:aa:ef:0b:a6:06:d0:b9:
23:6c:fd:0e:dd:74:6e:ff:34:a6:0f:24:ec:a5:70:
6c:7e:07:dc:e7:02:97:54:c3:db:45:d9:9a:f9:c4:
0b:70:82:12:52:d6:b5:72:a1:cc:ea:cb:96:00:99:
59:d3:20:0c:28:29:a1:1a:b6:ab:7d:e4:1f:03:35:
f4:65:e2:01:a7:d0:b0:4e:2d:fd:d5:f2:84:7f:9d:
83:90:c2:28:37:e7:87:9b:52:d9:ff:92:d9:28:06:
42:3c:d2:a7:57:6e:50:22:a2:32:07:6b:fe:54:72:
96:a4:db:75:56:8d:22:94:fb
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3Basic Constraints:
CA:FALSE
NetscapeComment:
OpenSSL Generated Certificate
X509v3Subject Key Identifier:
9E:C9:9A:33:FC:91:A9:34:CA:16:E5:79:5E:11:5B:BB:BA:61:65:75
X509v3Authority Key Identifier:
keyid:CC:33:C7:0E:59:10:F7:14:AF:F6:5E:85:9E:24:D6:81:14:3F:F5:47
Signature Algorithm: sha1WithRSAEncryption
c6:22:10:06:d2:98:fe:61:c0:cf:a8:9d:c7:50:c1:f9:9c:e8:
f9:a2:04:ba:d9:57:9c:8e:e0:59:51:cc:e3:06:21:ef:60:dd:
2c:6c:09:78:ec:cc:d5:46:26:90:e2:90:f5:3d:74:06:d7:3c:
be:b4:d4:a5:25:59:f0:eb:90:1a:37:d4:27:2b:fa:b3:7d:f2:
37:20:91:94:74:31:53:ff:3b:73:52:73:1c:9a:99:cd:c1:6f:
d2:0a:23:23:36:12:95:66:46:be:76:08:ae:e6:da:d8:6e:be:
84:ad:71:0f:ff:68:07:e2:e5:10:16:fc:13:85:fb:9f:b2:a4:
3b:89:9b:a3:7a:0d:5d:2a:f4:f2:a9:64:e9:38:88:12:2f:7b:
65:f9:18:58:61:93:68:d8:62:b3:4c:d7:6b:56:4e:49:01:a6:
3b:77:7a:40:77:d1:f6:c7:fc:7e:b8:e3:40:76:ea:0e:b2:0f:
c2:23:11:d5:c4:16:95:f7:5b:46:ac:44:aa:ae:c5:96:f0:d6:
96:d4:7d:12:59:d1:5e:ce:d0:52:dc:67:bf:23:c6:01:cd:85:
aa:45:7b:15:72:b0:a0:51:7b:30:ba:39:6c:f9:1a:6f:67:05:
c7:af:86:9e:04:70:b2:c8:91:9d:d8:a7:30:56:d0:ca:0d:f3:
58:9b:f4:f5
注意:每一个需要接收服务器发来的证书,并验证证书合法性的客户端主机,都必须拥有CA的证书才能进行。
我们可以在CA服务器查看索引数据库和serial文件来查看颁发的证书的简要信息:
[root@CA CA]# cat index.txt
V 21120528063310Z 01 unknown/C=CN/ST=HA/O=Test/OU=OPS/CN=stu1.test.com/emailAddress=stu1@test.com
[root@CA CA]# cat serial
02
四.吊销证书
1.在客户端获取证书的serial
[root@stu1 certs]# openssl x509 -in httpd.crt -noout -subject -serial
subject=/C=CN/ST=HA/O=Test/OU=OPS/CN=stu1.test.com/emailAddress=stu1@test.com
serial=01
2.根据证书持有者提供的serial和subject信息来与index.txt数据库文件中的信息比较是否一致
[root@CA CA]# cat index.txt
V 21120528063310Z 01 unknown /C=CN/ST=HA/O=Test/OU=OPS/CN=stu1.test.com/emailAddress=stu1@test.com
[root@CA CA]# ls newcerts/
pem
3.生成吊销证书的编号(如果第一次吊销)
[root@CA CA]# echo 01 >/etc/pki/CA/crlnumber
4.吊销证书
[root@CA CA]# openssl ca -revoke newcerts/01.pem
Using configuration from/etc/pki/tls/openssl.cnf
Revoking Certificate 01.
Data Base Updated
[root@CA CA]# cat index.txt
R 21120528063310Z 141208065437Z 01 unknown /C=CN/ST=HA/O=Test/OU=OPS/CN=stu1.test.com/emailAddress=stu1@test.com
5.更新证书吊销列表
[root@CA crl]# openssl ca -gencrl -out ca.crl
Using configuration from /etc/pki/tls/openssl.cnf
[root@CA crl]# file ca.crl
ca.crl: ASCII text
[root@CA crl]# openssl crl -in ca.crl -noout -text
Certificate Revocation List (CRL):
Version 2 (0x1)
Signature Algorithm: sha1WithRSAEncryption
Issuer: /C=CN/ST=HA/L=ZZ/O=Test/OU=OPS/CN=CA.test.com/emailAddress=ca@test.com
Last Update: Dec 8 06:57:56 2014GMT
Next Update: Jan 7 06:57:56 2015GMT
CRL extensions:
X509v3 CRL Number:
1
Revoked Certificates:
Serial Number: 01
Revocation Date: Dec 8 06:54:372014 GMT
Signature Algorithm: sha1WithRSAEncryption
85:37:14:3d:b8:aa:8a:82:39:fe:80:20:a0:ec:8f:15:a9:dd:
2e:06:e3:78:63:48:dd:ab:4f:fb:bd:c6:c4:ca:52:dc:d4:aa:
71:6f:70:92:50:bc:39:97:f9:ac:10:4b:50:44:cc:b7:c4:0d:
2c:3c:f2:ce:f5:1e:0a:b7:b0:3a:30:33:62:98:cd:d5:a9:ea:
1e:94:50:32:fc:81:4f:92:27:7e:e7:00:3e:ff:a9:d9:92:a4:
6f:11:7b:42:fe:b7:53:b3:e5:d4:4d:7d:c0:49:46:31:1a:8f:
39:62:95:0b:40:54:f1:ab:4b:80:89:d1:73:26:0f:ff:c7:fa:
12:21:34:c8:97:82:5b:09:e8:e8:42:21:5d:03:71:c3:50:d7:
6e:58:d5:56:b3:c9:89:68:14:6d:7f:09:68:de:9e:e6:ec:e3:
9d:e0:af:72:28:95:36:0f:32:2a:a5:bb:81:e8:63:46:ad:76:
f8:0b:02:df:a7:5e:ab:bf:b4:ae:45:20:1a:de:d6:db:dc:9c:
94:8e:32:e4:76:67:70:96:11:7b:13:12:f2:95:08:da:3f:6b:
68:ed:47:b0:af:a0:ee:de:86:af:66:c3:d6:42:30:8b:05:f8:
7a:45:6d:cc:f3:f4:fb:3c:b8:9a:e9:17:fc:92:18:52:fe:76:
7c:25:18:d6
至此,利用OpenSSL构建私有CA服务器就实验完毕!
本文出自 “龙之守护” 博客,请务必保留此出处http://sohudrgon.blog.51cto.com/3088108/1588146
利用OpenSSL构建私有CA
