首页 > 代码库 > Setup RHEVM Identity Management With IPA
Setup RHEVM Identity Management With IPA
The directory servers supported for use with Red Hat Enterprise Virtualization 3.3 are:
- Active Directory
- Identity Management (IDM)
- Red Hat Directory Server 9 (RHDS 9)
- OpenLDAP
From this article,you‘ll learn following:
- How to setup master IPA
- How to setup slave IPA
- How to attach a directory server to the RHEVM
Install IPA packages on master and slave
[root@ipa ~]# yum -y install ipa-server bind bind-dyndb-ldap firefox xorg-x11-xauth [root@slave ~]# yum -y install ipa-server bind bind-dyndb-ldap firefox xorg-x11-xauth
Configure master IPA server
[root@ipa ~]# ipa-server-install --setup-dns --forwarder=172.16.255.10
The log file for this installation can be found in /var/log/ipaserver-install.log
==============================================================================
This program will set up the IPA Server.
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the Network Time Daemon (ntpd)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
* Configure DNS (bind)
To accept the default shown in brackets, press the Enter key.
Existing BIND configuration detected, overwrite? [no]: yes
Enter the fully qualified domain name of the computer
on which you‘re setting up server software. Using the form
<hostname>.<domainname>
Example: master.example.com.
Server host name [ipa.xzxj.edu.cn]:
Warning: skipping DNS resolution of host ipa.xzxj.edu.cn
The domain name has been determined based on the host name.
Please confirm the domain name [xzxj.edu.cn]:
The kerberos protocol requires a Realm name to be defined.
This is typically the domain name converted to uppercase.
Please provide a realm name [XZXJ.EDU.CN]:
Certain directory server operations require an administrative user.
This user is referred to as the Directory Manager and has full access
to the Directory for system management tasks and will be added to the
instance of directory server created for IPA.
The password must be at least 8 characters long.
Directory Manager password:
Password (confirm):
The IPA server requires an administrative user, named ‘admin‘.
This user is a regular system account used for IPA server administration.
IPA admin password:
Password (confirm):
Do you want to configure the reverse zone? [yes]:
Please specify the reverse zone name [255.16.172.in-addr.arpa.]:
Using reverse zone 255.16.172.in-addr.arpa.
The IPA Master Server will be configured with:
Hostname: ipa.xzxj.edu.cn
IP address: 172.16.255.16
Domain name: xzxj.edu.cn
Realm name: XZXJ.EDU.CN
BIND DNS server will be configured to serve IPA domain with:
Forwarders: 172.16.255.10
Reverse zone: 255.16.172.in-addr.arpa.
Continue to configure the system with these values? [no]: yes
The following operations may take some minutes to complete.
Please wait until the prompt is returned.
Configuring NTP daemon (ntpd)
[1/4]: stopping ntpd
[2/4]: writing configuration
[3/4]: configuring ntpd to start on boot
[4/4]: starting ntpd
Done configuring NTP daemon (ntpd).
Configuring directory server for the CA (pkids): Estimated time 30 seconds
[1/3]: creating directory server user
[2/3]: creating directory server instance
[3/3]: restarting directory server
Done configuring directory server for the CA (pkids).
Configuring certificate server (pki-cad): Estimated time 3 minutes 30 seconds
[1/21]: creating certificate server user
[2/21]: creating pki-ca instance
[3/21]: configuring certificate server instance
[4/21]: disabling nonces
[5/21]: creating CA agent PKCS#12 file in /root
[6/21]: creating RA agent certificate database
[7/21]: importing CA chain to RA certificate database
[8/21]: fixing RA database permissions
[9/21]: setting up signing cert profile
[10/21]: set up CRL publishing
[11/21]: set certificate subject base
[12/21]: enabling Subject Key Identifier
[13/21]: setting audit signing renewal to 2 years
[14/21]: configuring certificate server to start on boot
[15/21]: restarting certificate server
[16/21]: requesting RA certificate from CA
[17/21]: issuing RA agent certificate
[18/21]: adding RA agent as a trusted user
[19/21]: configure certificate renewals
[20/21]: configure Server-Cert certificate renewal
[21/21]: Configure HTTP to proxy connections
Done configuring certificate server (pki-cad).
Configuring directory server (dirsrv): Estimated time 1 minute
[1/38]: creating directory server user
[2/38]: creating directory server instance
[3/38]: adding default schema
[4/38]: enabling memberof plugin
[5/38]: enabling winsync plugin
[6/38]: configuring replication version plugin
[7/38]: enabling IPA enrollment plugin
[8/38]: enabling ldapi
[9/38]: disabling betxn plugins
[10/38]: configuring uniqueness plugin
[11/38]: configuring uuid plugin
[12/38]: configuring modrdn plugin
[13/38]: enabling entryUSN plugin
[14/38]: configuring lockout plugin
[15/38]: creating indices
[16/38]: enabling referential integrity plugin
[17/38]: configuring ssl for ds instance
[18/38]: configuring certmap.conf
[19/38]: configure autobind for root
[20/38]: configure new location for managed entries
[21/38]: restarting directory server
[22/38]: adding default layout
[23/38]: adding delegation layout
[24/38]: adding replication acis
[25/38]: creating container for managed entries
[26/38]: configuring user private groups
[27/38]: configuring netgroups from hostgroups
[28/38]: creating default Sudo bind user
[29/38]: creating default Auto Member layout
[30/38]: adding range check plugin
[31/38]: creating default HBAC rule allow_all
[32/38]: Upload CA cert to the directory
[33/38]: initializing group membership
[34/38]: adding master entry
[35/38]: configuring Posix uid/gid generation
[36/38]: enabling compatibility plugin
[37/38]: tuning directory server
[38/38]: configuring directory to start on boot
Done configuring directory server (dirsrv).
Configuring Kerberos KDC (krb5kdc): Estimated time 30 seconds
[1/10]: adding sasl mappings to the directory
[2/10]: adding kerberos container to the directory
[3/10]: configuring KDC
[4/10]: initialize kerberos container
[5/10]: adding default ACIs
[6/10]: creating a keytab for the directory
[7/10]: creating a keytab for the machine
[8/10]: adding the password extension to the directory
[9/10]: starting the KDC
[10/10]: configuring KDC to start on boot
Done configuring Kerberos KDC (krb5kdc).
Configuring kadmin
[1/2]: starting kadmin
[2/2]: configuring kadmin to start on boot
Done configuring kadmin.
Configuring ipa_memcached
[1/2]: starting ipa_memcached
[2/2]: configuring ipa_memcached to start on boot
Done configuring ipa_memcached.
Configuring the web interface (httpd): Estimated time 1 minute
[1/13]: setting mod_nss port to 443
[2/13]: setting mod_nss password file
[3/13]: enabling mod_nss renegotiate
[4/13]: adding URL rewriting rules
[5/13]: configuring httpd
[6/13]: setting up ssl
[7/13]: setting up browser autoconfig
[8/13]: publish CA cert
[9/13]: creating a keytab for httpd
[10/13]: clean up any existing httpd ccache
[11/13]: configuring SELinux for httpd
[12/13]: restarting httpd
[13/13]: configuring httpd to start on boot
Done configuring the web interface (httpd).
Applying LDAP updates
Restarting the directory server
Restarting the KDC
Configuring DNS (named)
[1/9]: adding DNS container
[2/9]: setting up our zone
[3/9]: setting up reverse zone
[4/9]: setting up our own record
[5/9]: setting up kerberos principal
[6/9]: setting up named.conf
[7/9]: restarting named
[8/9]: configuring named to start on boot
[9/9]: changing resolv.conf to point to ourselves
Done configuring DNS (named).
Global DNS configuration in LDAP server is empty
You can use ‘dnsconfig-mod‘ command to set global DNS options that
would override settings in local named.conf files
Restarting the web server
==============================================================================
Setup complete
Next steps:
1. You must make sure these network ports are open:
TCP Ports:
* 80, 443: HTTP/HTTPS
* 389, 636: LDAP/LDAPS
* 88, 464: kerberos
* 53: bind
UDP Ports:
* 88, 464: kerberos
* 53: bind
* 123: ntp
2. You can now obtain a kerberos ticket using the command: ‘kinit admin‘
This ticket will allow you to use the IPA tools (e.g., ipa user-add)
and the web user interface.
Be sure to back up the CA certificate stored in /root/cacert.p12
This file is required to create replicas. The password for this
file is the Directory Manager passwordAfter configure,you need to get a kerberos ticket:
[root@ipa ~]# kinit admin Password for admin@XZXJ.EDU.CN: [root@ipa ~]# klist Ticket cache: FILE:/tmp/krb5cc_0 Default principal: admin@XZXJ.EDU.CN Valid starting Expires Service principal 05/17/14 12:18:59 05/18/14 12:18:56 krbtgt/XZXJ.EDU.CN@XZXJ.EDU.CN
Setting up a replica
[root@ipa ~]# ipa-replica-prepare slave.xzxj.edu.cn Directory Manager (existing master) password:******** Preparing replica for slave.xzxj.edu.cn from ipa.xzxj.edu.cn Creating SSL certificate for the Directory Server Creating SSL certificate for the dogtag Directory Server Creating SSL certificate for the Web Server Exporting RA certificate Copying additional files Finalizing configuration Packaging replica information into /var/lib/ipa/replica-info-slave.xzxj.edu.cn.gpg [root@ipa ~]# scp /var/lib/ipa/replica-info-slave.xzxj.edu.cn.gpg slave:/root
Configure slave IPA server
[root@slave ~]# ipa-replica-install --setup-dns --forwarder=172.16.255.10 replica-info-slave.xzxj.edu.cn.gpg Directory Manager (existing master) password:******* Run connection check to master Check connection from replica to remote master ‘ipa.xzxj.edu.cn‘: Directory Service: Unsecure port (389): OK Directory Service: Secure port (636): OK Kerberos KDC: TCP (88): OK Kerberos Kpasswd: TCP (464): OK HTTP Server: Unsecure port (80): OK HTTP Server: Secure port (443): OK The following list of ports use UDP protocol and would need to be checked manually: Kerberos KDC: UDP (88): SKIPPED Kerberos Kpasswd: UDP (464): SKIPPED Connection from replica to master is OK. Start listening on required ports for remote master check Get credentials to log in to remote master admin@XZXJ.EDU.CN password: Execute check on remote master Check connection from master to remote replica ‘slave.xzxj.edu.cn‘: Directory Service: Unsecure port (389): OK Directory Service: Secure port (636): OK Kerberos KDC: TCP (88): OK Kerberos KDC: UDP (88): OK Kerberos Kpasswd: TCP (464): OK Kerberos Kpasswd: UDP (464): OK HTTP Server: Unsecure port (80): OK HTTP Server: Secure port (443): OK Connection from master to replica is OK. Connection check OK Configuring NTP daemon (ntpd) [1/4]: stopping ntpd [2/4]: writing configuration [3/4]: configuring ntpd to start on boot [4/4]: starting ntpd Done configuring NTP daemon (ntpd). Configuring directory server (dirsrv): Estimated time 1 minute [1/31]: creating directory server user [2/31]: creating directory server instance [3/31]: adding default schema [4/31]: enabling memberof plugin [5/31]: enabling winsync plugin [6/31]: configuring replication version plugin [7/31]: enabling IPA enrollment plugin [8/31]: enabling ldapi [9/31]: disabling betxn plugins [10/31]: configuring uniqueness plugin [11/31]: configuring uuid plugin [12/31]: configuring modrdn plugin [13/31]: enabling entryUSN plugin [14/31]: configuring lockout plugin [15/31]: creating indices [16/31]: enabling referential integrity plugin [17/31]: configuring ssl for ds instance [18/31]: configuring certmap.conf [19/31]: configure autobind for root [20/31]: configure new location for managed entries [21/31]: restarting directory server [22/31]: setting up initial replication Starting replication, please wait until this has completed. Update in progress Update in progress Update in progress Update in progress Update succeeded [23/31]: adding replication acis [24/31]: setting Auto Member configuration [25/31]: enabling S4U2Proxy delegation [26/31]: initializing group membership [27/31]: adding master entry [28/31]: configuring Posix uid/gid generation [29/31]: enabling compatibility plugin [30/31]: tuning directory server [31/31]: configuring directory to start on boot Done configuring directory server (dirsrv). Configuring Kerberos KDC (krb5kdc): Estimated time 30 seconds [1/9]: adding sasl mappings to the directory [2/9]: writing stash file from DS [3/9]: configuring KDC [4/9]: creating a keytab for the directory [5/9]: creating a keytab for the machine [6/9]: adding the password extension to the directory [7/9]: enable GSSAPI for replication [8/9]: starting the KDC [9/9]: configuring KDC to start on boot Done configuring Kerberos KDC (krb5kdc). Configuring kadmin [1/2]: starting kadmin [2/2]: configuring kadmin to start on boot Done configuring kadmin. Configuring ipa_memcached [1/2]: starting ipa_memcached [2/2]: configuring ipa_memcached to start on boot Done configuring ipa_memcached. Configuring the web interface (httpd): Estimated time 1 minute [1/12]: setting mod_nss port to 443 [2/12]: setting mod_nss password file [3/12]: enabling mod_nss renegotiate [4/12]: adding URL rewriting rules [5/12]: configuring httpd [6/12]: setting up ssl [7/12]: publish CA cert [8/12]: creating a keytab for httpd [9/12]: clean up any existing httpd ccache [10/12]: configuring SELinux for httpd [11/12]: restarting httpd [12/12]: configuring httpd to start on boot Done configuring the web interface (httpd). Applying LDAP updates Restarting the directory server Restarting the KDC Using reverse zone 255.16.172.in-addr.arpa. Configuring DNS (named) [1/8]: adding NS record to the zone [2/8]: setting up reverse zone [3/8]: setting up our own record [4/8]: setting up kerberos principal [5/8]: setting up named.conf [6/8]: restarting named [7/8]: configuring named to start on boot [8/8]: changing resolv.conf to point to ourselves Done configuring DNS (named). Global DNS configuration in LDAP server is empty You can use ‘dnsconfig-mod‘ command to set global DNS options that would override settings in local named.conf files Restarting the web server //Get a Kerberos ticket [root@slave ~]# kinit admin Password for admin@XZXJ.EDU.CN: [root@slave ~]# klist Ticket cache: FILE:/tmp/krb5cc_0 Default principal: admin@XZXJ.EDU.CN Valid starting Expires Service principal 05/17/14 15:20:06 05/18/14 15:20:03 krbtgt/XZXJ.EDU.CN@XZXJ.EDU.CN
Some adjustment
Unfortunately the default shell for new users is /bin/sh, which should probably be changed.
[root@slave ~]# ipa config-mod --defaultshell=/bin/bash Maximum username length: 32 Home directory base: /home Default shell: /bin/bash Default users group: ipausers Default e-mail domain: xzxj.edu.cn Search time limit: 2 Search size limit: 100 User search fields: uid,givenname,sn,telephonenumber,ou,title Group search fields: cn,description Enable migration mode: FALSE Certificate Subject base: O=XZXJ.EDU.CN Password Expiration Notification (days): 4 Password plugin features: AllowNThash SELinux user map order: guest_u:s0$xguest_u:s0$user_u:s0$staff_u:s0-s0:c0.c1023$unconfined_u:s0-s0:c0.c1023 Default SELinux user: unconfined_u:s0-s0:c0.c1023 Default PAC types: MS-PAC
Testing the replication
Login in to ipa.xzxj.edu.cn and add a new user:
[root@ipa ~]# ipa user-add candon First name: aaaa Last name: bb ------------------- Added user "candon" ------------------- User login: candon First name: jacky Last name: lee Full name: jacky lee Display name: jacky lee Initials: jl Home directory: /home/candon GECOS field: jacky lee Login shell: /bin/bash Kerberos principal: candon@XZXJ.EDU.CN Email address: candon@xzxj.edu.cn UID: 1229200001 GID: 1229200001 Password: False Kerberos keys available: False [root@ipa named]# ipa passwd candon New Password: Enter New Password again to verify: ----------------------------------------- Changed password for "candon@XZXJ.EDU.CN" -----------------------------------------
Now,you can check if the user is really available on both servers by following a ldapsearch command:
[root@slave ~]# ldapsearch -x -b "dc=xzxj,dc=edu,dc=cn" uid=candon
Set up a IPA client
[root@TestOS01 ~]# yum install ipa-client
[root@TestOS01 ~]# ipa-client-install -p admin
DNS domain ‘xzxj.edu.cn‘ is not configured for automatic KDC address lookup.
KDC address will be set to fixed value.
Discovery was successful!
Hostname: testos01.xzxj.edu.cn
Realm: XZXJ.EDU.CN
DNS Domain: xzxj.edu.cn
IPA Server: ipa.xzxj.edu.cn
BaseDN: dc=xzxj,dc=edu,dc=cn
Continue to configure the system with these values? [no]: yes
Synchronizing time with KDC...
Unable to sync time with IPA NTP server, assuming the time is in sync. Please check that 123 UDP port is opened.
Password for admin@XZXJ.EDU.CN:
Successfully retrieved CA cert
Subject: CN=Certificate Authority,O=XZXJ.EDU.CN
Issuer: CN=Certificate Authority,O=XZXJ.EDU.CN
Valid From: Fri May 16 20:13:21 2014 UTC
Valid Until: Tue May 16 20:13:21 2034 UTC
Enrolled in IPA realm XZXJ.EDU.CN
Created /etc/ipa/default.conf
New SSSD config will be created
Configured /etc/sssd/sssd.conf
Configured /etc/krb5.conf for IPA realm XZXJ.EDU.CN
trying https://ipa.xzxj.edu.cn/ipa/xml
Forwarding ‘env‘ to server u‘https://ipa.xzxj.edu.cn/ipa/xml‘
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_dsa_key.pub
Forwarding ‘host_mod‘ to server u‘https://ipa.xzxj.edu.cn/ipa/xml‘
Could not update DNS SSHFP records.
SSSD enabled
Configured /etc/openldap/ldap.conf
NTP enabled
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config
Client configuration complete.Test Testing the login
[root@ipa ~]# ssh 172.16.255.151 -l candon candon@172.16.255.151‘s password: Password expired. Change your password now. Kickstarted on 2014-05-01 WARNING: Your password has expired. You must change your password now and login again! Changing password for user candon. Current Password: New password: Retype new password: passwd: all authentication tokens updated successfully. [root@ipa ~]# ssh 172.16.255.151 -l candon candon@172.16.255.151‘s password: -bash-4.1$
Configure RHEVM by redhat-manage-domains command
[root@rhevm ~]# rhevm-manage-domains -action=add -addPermissions -domain=xzxj.edu.cn -user=admin -interactive -provider=IPA Enter password: Successfully added domain xzxj.edu.cn. oVirt Engine restart is required in order for the changes to take place (service ovirt-engine restart). Manage Domains completed successfully [root@rhevm ~]# service ovirt-engine restart Stopping oVirt Engine: [ OK ] Starting oVirt Engine: [ OK ]
Lists the current configuration
[root@rhevm ~]# rhevm-manage-domains -action=list
Domain: xzxj.edu.cn
User name: admin@XZXJ.EDU.CN
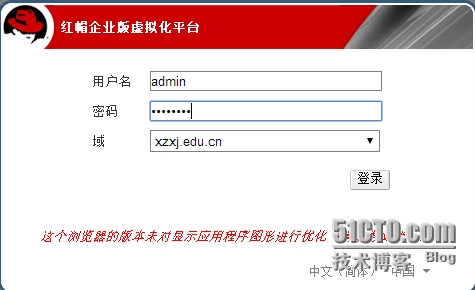
Manage Domains completed successfullyLogin in rhevm web interface by user admin@xzxj.edu.cn
本文出自 “candon123” 博客,谢绝转载!
