首页 > 代码库 > 三、加密算法与openssl的使用
三、加密算法与openssl的使用
3.1、加密算法的分类
加密是以某种特殊的算法改变原有的信息数据使得未授权的用户即使获得了已加密的信息但因不知解密的方法仍然无法了解信息的内容。在互联网上对数据的加密主要是保证三个方面内容数据的保密性、完整性以及对方的身份验证。
加密类型分为两种对称加密与非对称加密。
对称加密双方采用共同密常见算法有DES、3DES、AES等 特性加密、解密使用同一个密钥将原始数据分割成固定大小的块逐个进行加密。 缺陷密钥过多密钥分发。 |
非对称加密密钥是成对儿出现常见算法有RSA, DSA, ELGama等 公钥公开给所有人pubkey 私钥自己留存必须保证其私密性secret key 特点用公钥加密的数据只能使用与之配对儿的私钥解密 主要应用 数字签名主要在于让接收方确认发送方身份 密钥交换发送方用对方的公钥加密一个对称密钥并发送给对方 数据加密加密数据信息 |
单向加密常见算法MD5,SHA1等。 只能加密不能解密提取数据指纹 特性定长输出、雪崩效应原数据的微小改变导致加密后的数据指纹完全变化。 |
在互联网上进行上方的数据交互时为了保证数据的保密性与完整性以及确认对方的身份需要进行一套复杂的加密算法。
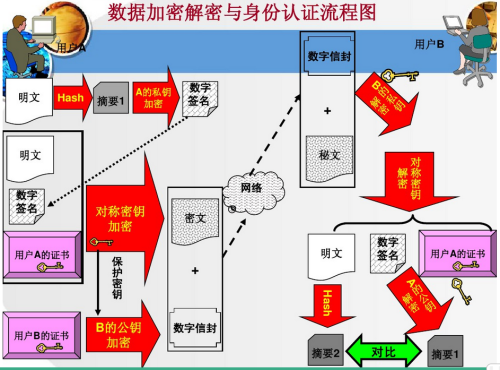
1、对需要发送的数据采用单向加密算法提取摘要信息利用A的私钥加密摘要信息加密后的摘要信息成为数字签名放在明文之后。 2、在利用A的私密加密成为密文。 3、再使用对称加密使用B公钥加密密码成为数据信封完成保密性。 |
3.2、SSL协议与openssl
SSL(Secure Sockets Layer 安全套接层),及其继任者传输层安全Transport Layer SecurityTLS是为网络通信提供安全及数据完整性的一种安全协议。TLS与SSL在传输层对网络连接进行加密。主要提供的服务为认证用户和服务器确保数据发送到正确的客户机和服务器加密数据以防止数据中途被窃取维护数据的完整性确保数据在传输过程中不被改变。
OpenSSL 是一个安全套接字层密码库囊括主要的密码算法、常用的密钥和证书封装管理功能及SSL协议并提供丰富的应用程序供测试或其它目的使用。
Openssl的组成主要可以分为三个部分
libcrypto: 加密库
libssl: TLS/SSL实现基于会话的、实现身份认证、数据机密性和会话完整性的TLS/SSL库
openssl: 多用途命令行工具实现加密的工具。
openssl命令的用法
openssl command [ command_opts ] [ command_args ] openssl [ list-standard-commands | list-message-digest-commands | list-cipher-commands | list-cipher-algorithms | list-message-digest-algorithms | list-public-key- algorithms]
STANDARD COMMANDS asn1parse、ca、ciphers、cms、crl、crl2pkcs7、dgst、dh、dhparam、dsa、dsaparam ec ecparam enc engine errstr gendh gendsa genpkey genrsa nseq ocsp passwd pkcs12 pkcs7 pkey pkeyparam pkeyutl rand req rsa rsautl s_client s_server s_time sess_id smime speed spkac ts verify x509 MESSAGE DIGEST COMMANDS md2 md5 mdc2 rmd160 sha sha1 sha224 sha256 sha384 sha512 ENCODING AND CIPHER COMMANDS base64 Base64 Encoding bf bf-cbc bf-cfb bf-ecb bf-ofb cast cast-cbc cast5-cbc cast5-cfb cast5-ecb cast5-ofb des des-cbc des-cfb des-ecb des-ede des-ede-cbc des-ede-cfb des-ede-ofb des-ofb des3 desx des-ede3 des-ede3-cbc des-ede3-cfb des-ede3-ofb idea idea-cbc idea-cfb idea-ecb idea-ofb rc2 rc2-cbc rc2-cfb rc2-ecb rc2-ofb rc4 rc5 rc5-cbc rc5-cfb rc5-ecb rc5-ofb |
对称加密
openssl enc -des3 -a -salt -in /path/to/input_file -out cipher_file #加密 openssl enc -d -des3 -a -salt -in /path/to/cipher_file -out clear_file #解密 |
[root@mylinux home]# cat test.py #查看文件内容 #!/usr/bin/python3 def add(num1,num2): ‘‘‘ >>> add(12,23) 35 ‘‘‘ return num1+num2 if __name__ == ‘__main__‘: import doctest doctest.testmod() [root@mylinux home]# openssl enc -des3 -a -salt -in test.py -out cipher.py #对文件加密 enter des-ede3-cbc encryption password: Verifying - enter des-ede3-cbc encryption password: [root@mylinux home]# cat cipher.py #加密后的文档 U2FsdGVkX1/UmevKTgGU4h+9lzx024oU9uI9ifaddQZ008Sg+FGEpFVXMZe77/NH REcx8lgonK+05Qilx9lbFtIO0qY8jsEQF9yyiQEF4H0sYzIVnh5W5fq6k3RvZRfF pPaIw0L3OMdj+N8i5hxLsjusD/aPvpAtzial/VDOFZ8TJulXotzpRMjUvlKum8Og MUxzTNwAHKZbAaPL2vdQoPpvLuM3bL2VYTkJyn/tWv0= [root@mylinux home]# openssl enc -d -des3 -a -salt -in cipher.py -out test1.py #解密 enter des-ede3-cbc decryption password: [root@mylinux home]# cat test1.py #解密后的文档 #!/usr/bin/python3 def add(num1,num2): ‘‘‘ >>> add(12,23) 35 ‘‘‘ return num1+num2 if __name__ == ‘__main__‘: import doctest doctest.testmod() [root@mylinux home]#
单向加密
openssl dgst [-md5|-md4|-md2|-sha1|-sha|-mdc2|-ripemd160|-dss1] [-out filename] somefile |
[root@mylinux home]# ls date loganalyzer-3.6.6 python_web shell wswp-code dow.zip __pycache__ samba test.py [root@mylinux home]# openssl md5 test.py #提取test.py的md5特征码 MD5(test.py)= cafc9ca93649c2b9d67f33075402ce24
公钥加密公钥加密(一般不会用来加密数据)私钥解密数据
密钥交换获得对方的公钥、数据加密使用对方的公钥、身份认证使用自己的私钥
openssl genrsa -out /PATH/TO/KEYFILENAME NUMBITS 生成私钥rsa openssl rsa -in /PATH/TO/KEYFILENAME -pubout提取公钥 |
[root@mylinux home]# openssl genrsa -out private.pem 2048 #生成私钥
Generating RSA private key, 2048 bit long modulus
..........................................................+++
.................................................+++
e is 65537 (0x10001)
[root@mylinux home]# openssl rsa -in private.pem -pubout -out pub.pem #私钥中提取公钥
writing RSA key
[root@mylinux home]# ls
cipher.py dow.zip private.pem __pycache__ samba test.py
date loganalyzer-3.6.6 pub.pem python_web shell wswp-code
[root@mylinux home]# cat date
ls -l
date
[root@mylinux home]# openssl rsautl -encrypt -in date -inkey pub.pem -pubin -out date.en #利用公钥加密date文件
[root@mylinux home]# cat date.en #加密后文件
)L:vsnWiyc$[%v4,ogqNwktU1]W}YB&u$q {F[root@mylinux home]#
[root@mylinux home]# openssl rsautl -decrypt -in date.en -inkey private.pem -out date.de #使用私钥解密文件
[root@mylinux home]# cat date.de #解密后文件
ls -l
date3.3、签发证书与CA
在网上通信时,通常需要将数据进行加密,对于一个使用了SSL的web网站拥有者必须要产生一个CSR(Certificate Signing Request,签发证书请求),CSR是一个数字文件,其中包含一个公钥和一个公司名称,‘证书‘必须由一个称为CA(Certificate Authority,证书授权机构)的可信来源签发。
CA服务器的生成:
1、确定CA的工作目录
[root@promote CA]# vim /etc/pki/tls/openssl.cnf certificate = $dir/cacert.pem # The CA certificate serial = $dir/serial # The current serial number crlnumber = $dir/crlnumber # the current crl number # must be commented out to leave a V1 CRL ... [ CA_default ] dir = /etc/pki/CA # Where everything is kept #工作目录 ...
2、自签证书
[root@promote ~]# cd /etc/pki/CA/ [root@promote CA]# ls certs crl newcerts private [root@promote CA]# umask 077 [root@promote CA]# openssl genrsa -out private/cakey.pem 2048 #生成私钥 Generating RSA private key, 2048 bit long modulus .......................+++ ...............................................................+++ e is 65537 (0x10001) [root@promote CA]# openssl rsa -in private/cakey.pem -text -noout #可以查看公钥 Private-Key: (2048 bit) modulus: 00:a3:a5:32:18:d8:3f:8a:6a:b7:8c:f2:3f:85:b9: d5:ea:d4:21:47:c3:11:9c:1b:65:22:b8:02:ac:2f: 51:e0:d5:0a:bd:e1:d9:5c:de:cd:80:3a:3a:b3:15: c0:38:db:b4:b7:4d:34:32:6f:7a:90:85:8a:b5:68: c2:04:9c:71:e9:0f:5a:e4:06:77:93:ef:5b:be:32: ba:0f:d8:aa:90:19:b0:2f:f2:13:06:a2:7b:a3:72: c7:28:34:a3:d9:0f:d7:35:1b:28:4e:73:cf:5c:ca: 7e:4d:56:c1:56:82:83:c2:c7:d9:31:f5:9a:0d:9a: 53:63:21:40:99:81:ee:6a:80:37:47:4a:b0:4f:5e: 7c:3b:e1:79:85:de:99:d7:85:fd:f8:5c:c8:c7:16: 7f:d3:b6:36:1e:54:08:be:7a:27:a2:3c:c4:7c:c2: 76:e8:26:56:17:24:3c:f4:cb:ba:80:97:f1:17:11: 6b:2d:b5:93:df:04:54:14:dc:1f:cf:49:43:31:f7: fe:ae:99:a0:34:cc:d1:85:61:c5:55:e7:27:4b:60: 3d:6e:a4:71:1a:43:58:9b:3f:27:29:66:04:41:c4: 7e:41:bb:08:82:be:ec:68:56:37:b1:fa:7d:53:09: 10:8a:4c:39:81:28:c2:83:33:88:63:f0:3e:bb:f4: bb:37 ... [root@promote CA]# openssl req -x509 -new -key private/cakey.pem -out cacert.pem -days 365 #生成证书 You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.‘, the field will be left blank. ----- Country Name (2 letter code) [XX]:CH State or Province Name (full name) []:AH Locality Name (eg, city) [Default City]:AQ Organization Name (eg, company) [Default Company Ltd]:UJS Organizational Unit Name (eg, section) []: Common Name (eg, your name or your server‘s hostname) []: Email Address []:
3、创建需要的文件:
[root@promote CA]# touch index.txt serial crlnumber [root@promote CA]# echo 01 > serial [root@promote CA]# ls cacert.pem certs crl crlnumber index.txt newcerts private serial
证书申请方:
1、为某服务生成密钥:
[root@promote CA]# cd /etc/ssh/ [root@promote ssh]# ls moduli ssh_host_dsa_key ssh_host_key.pub ssh_config ssh_host_dsa_key.pub ssh_host_rsa_key sshd_config ssh_host_key ssh_host_rsa_key.pub [root@promote ssh]# mkdir ssh [root@promote ssh]# cd ssh [root@promote ssh]# umask 077 [root@promote ssh]# openssl genrsa 1024 >ssh.key #生成秘钥 Generating RSA private key, 1024 bit long modulus ....................++++++ .............++++++ e is 65537 (0x10001) [root@promote ssh]# openssl req -new -key ssh.key -out ssh.csr #生成证书签署请求 You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.‘, the field will be left blank. ----- Country Name (2 letter code) [XX]:CA State or Province Name (full name) []:AH Locality Name (eg, city) [Default City]:AQ Organization Name (eg, company) [Default Company Ltd]:UJS Organizational Unit Name (eg, section) []: Common Name (eg, your name or your server‘s hostname) []:www.mylinux.com Email Address []: Please enter the following ‘extra‘ attributes to be sent with your certificate request A challenge password []:123456 An optional company name []:mylinux
2、将此请求通过某方式传递给CA服务器
#scp ssh.csr USERNAME@HOST:/path/to/somewhere(复制到CA服务器)
3、CA签署证书(在CA服务器上操作),再发送给申请方
[root@promote ssh]# openssl ca -in ssh.csr -out ssh.crt -days 365 Using configuration from /etc/pki/tls/openssl.cnf Check that the request matches the signature Signature ok Certificate Details: Serial Number: 1 (0x1) Validity Not Before: May 16 20:22:46 2017 GMT Not After : May 16 20:22:46 2018 GMT Subject: countryName = CA stateOrProvinceName = AH organizationName = UJS commonName = www.mylinux.com X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: 02:46:26:FF:10:D9:7F:8A:70:68:41:52:E1:6F:35:46:7C:FF:A6:BB X509v3 Authority Key Identifier: keyid:0A:04:7A:44:C6:8B:69:FD:7E:B0:F3:E4:5A:90:F4:DE:83:9B:A1:95 Certificate is to be certified until May 16 20:22:46 2018 GMT (365 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated [root@promote ssh]# ls ssh.crt ssh.csr ssh.key # scp vsftpd.crt USERNAME@HOST:/path/to/somewhere(复制到申请方)
openssl中有各后缀名的文件的含义
.key格式:私有的密钥
.crt格式:证书文件,certificate的缩写
.csr格式:证书签名请求(证书请求文件),含有公钥信息,certificate signing request的缩写
.crl格式:证书吊销列表,Certificate Revocation List的缩写
.pem格式:用于导出,导入证书时候的证书的格式,有证书开头,结尾的格式
本文出自 “随风而飘” 博客,请务必保留此出处http://yinsuifeng.blog.51cto.com/10173491/1926427
三、加密算法与openssl的使用
